Elevate your admin requests.
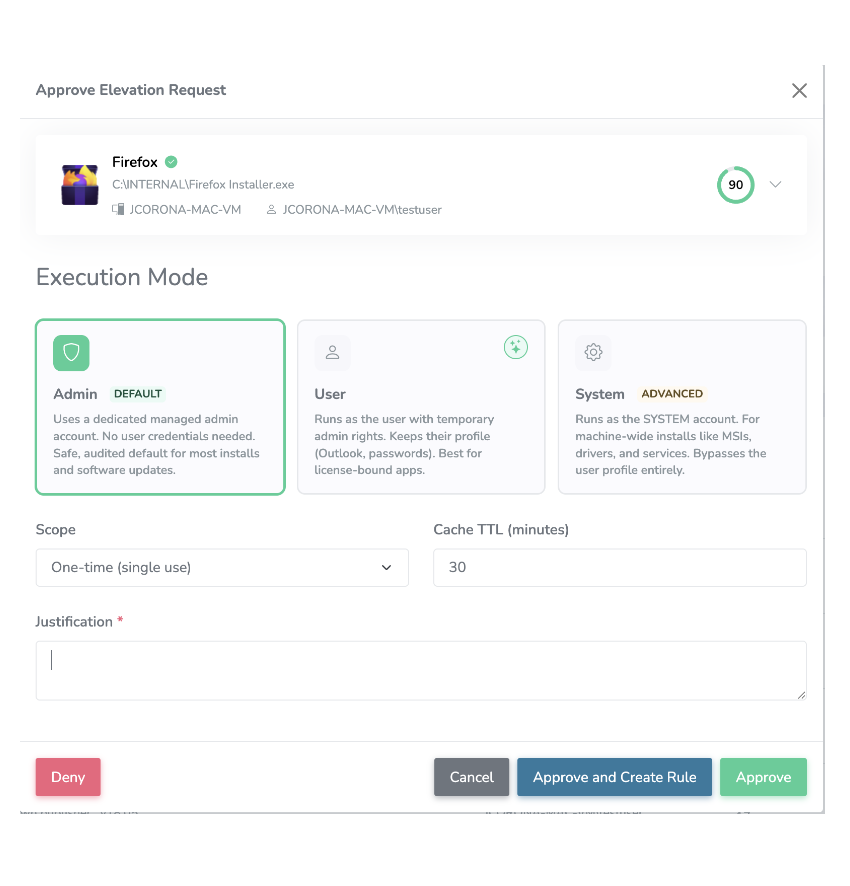
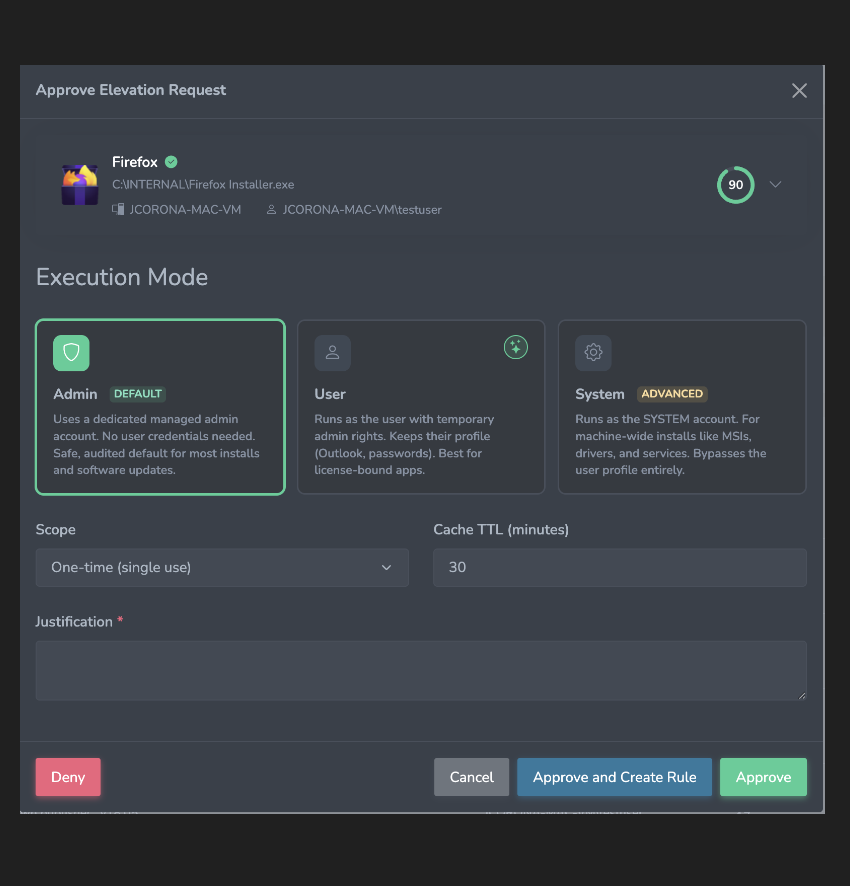
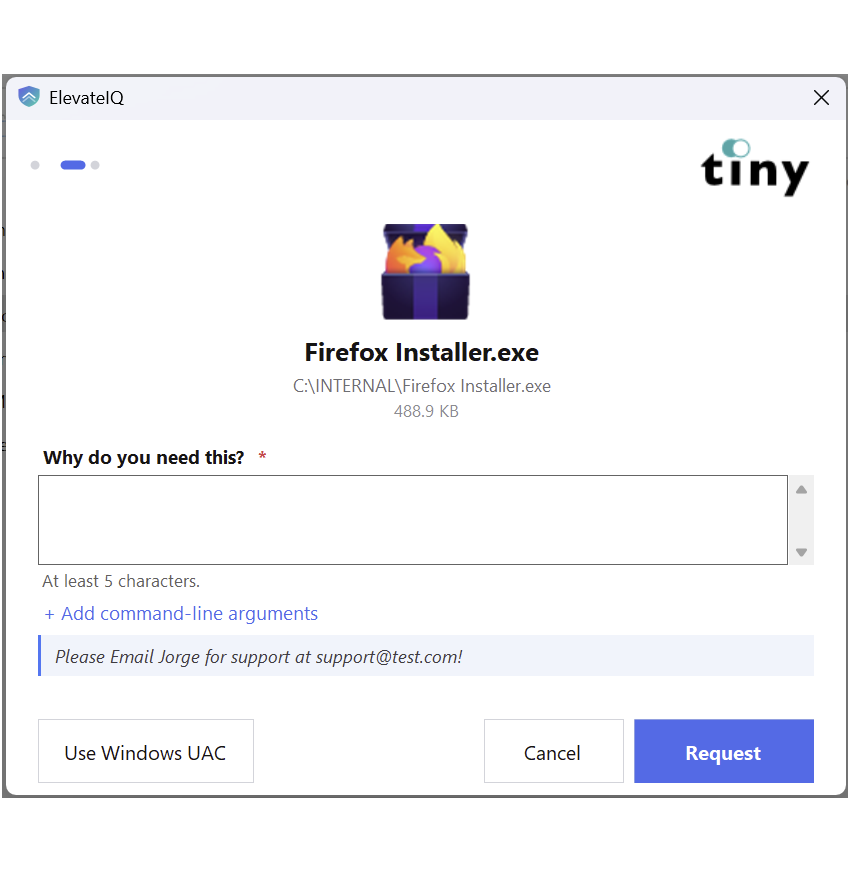
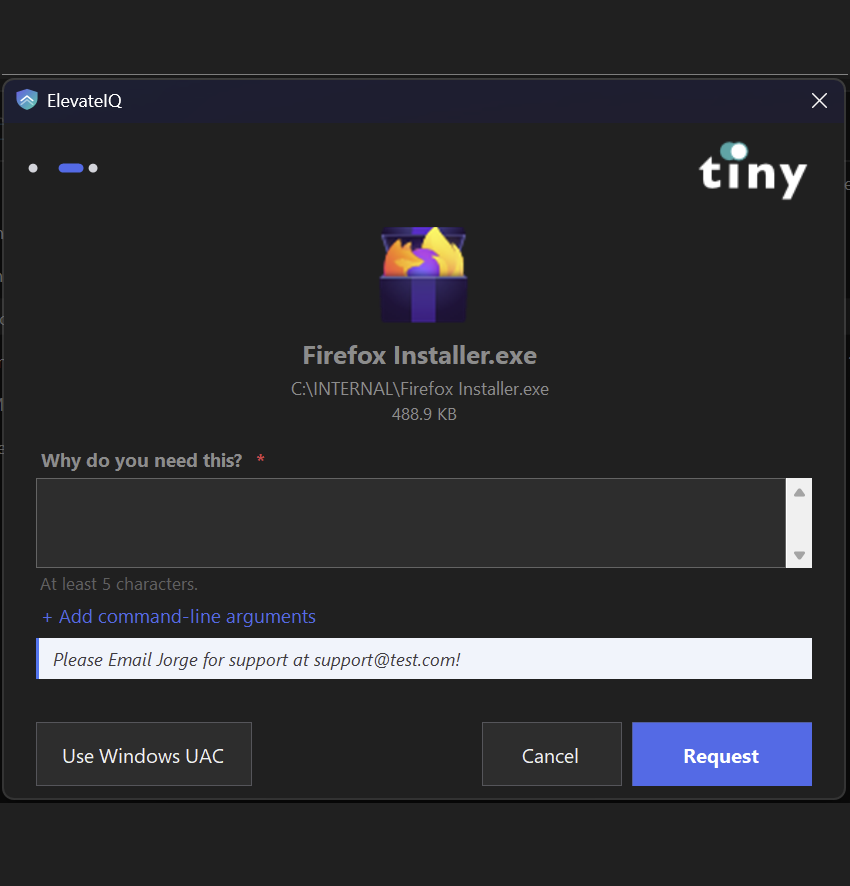
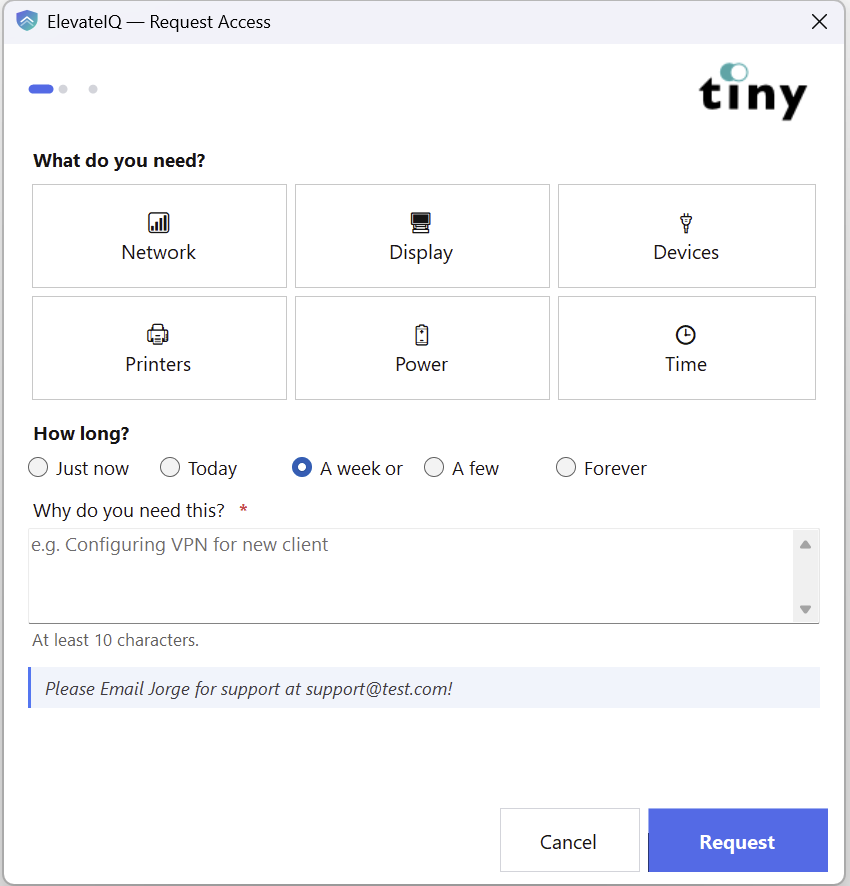
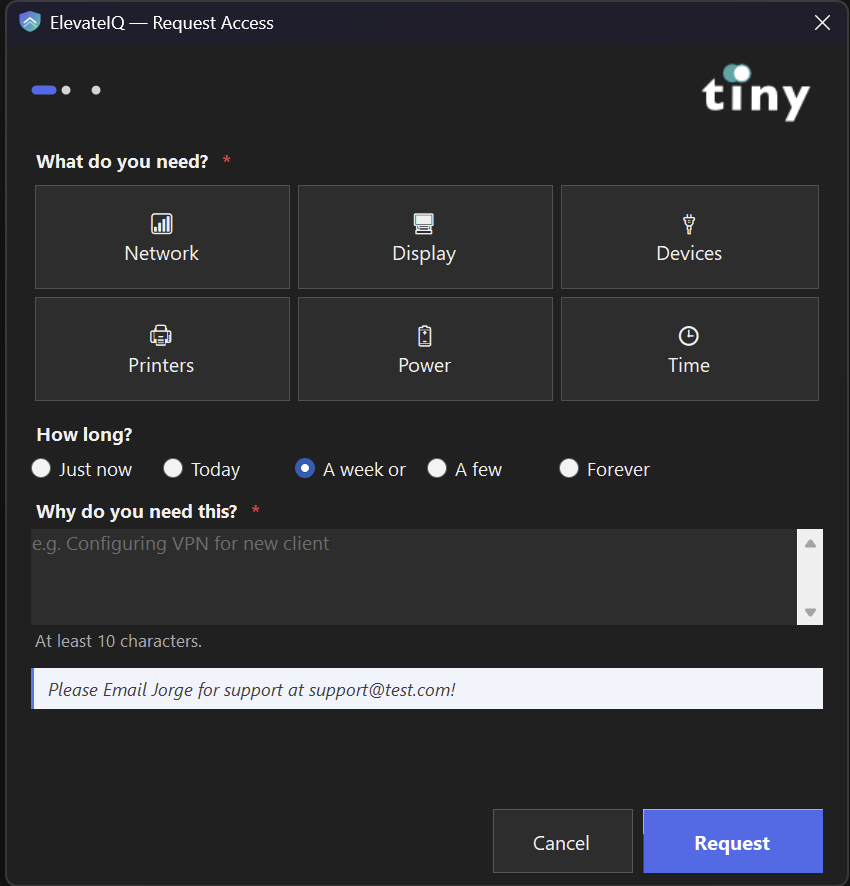
Need to install an app or change a network setting? Verify it's you with a quick MFA tap, write one line about why, and you're done — usually in seconds. No shared admin passwords, no waiting on IT, no dead-end "you don't have permission" dialogs. Your IT team still owns the rules; you just stop being the bottleneck.